Our Approach

Proxy Protection
The first step in our approach is to immediately protect your website DNS, because that becomes the 1st point of failure in case attack targets the DNS cluster. Our proxy protection makes sure that your website goes behind our protected network, so it’s public IP is not exposed. By anonymizing the IP, we are adding an additional layer of security which the attacker needs to crack.
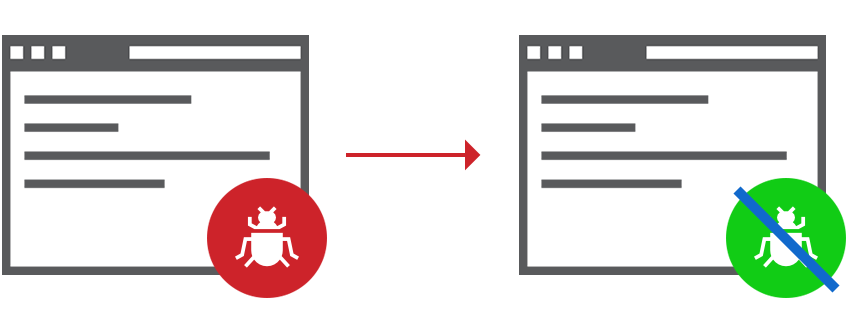
Website Protection
Our second layer of protection is to directly protect your website from all cyber attacks, including Application Layer 7 attacks. We use Web Application Firewall (WAF) to provide this kind of DDoS attack. The WAF itself is able to cover majority of the cyber attacks including OWASP Top10 vulnerabilities (SQL Injection, XML External Entries XXE, Cross Site Scripting XSS, Insecure Deserialization, Broken Access Control etc.), protection against Zero Day Vulnerability, fulfilling PCI DSS Compliance requirement 6.6, Threat Blocking and Privacy Features.

Server Protection
Our third layer of protection is to directly protect your server infrastructure from all kinds of DDoS attacks. Featuring network layer protection, the server encompasses all aspects. Our server is provisioned on a secure network with 100% DDoS Protection. We offer a wide variety of servers ranging from Entry level series to Powerful multi-core processors, with SSD storage, redundant network and full server management.
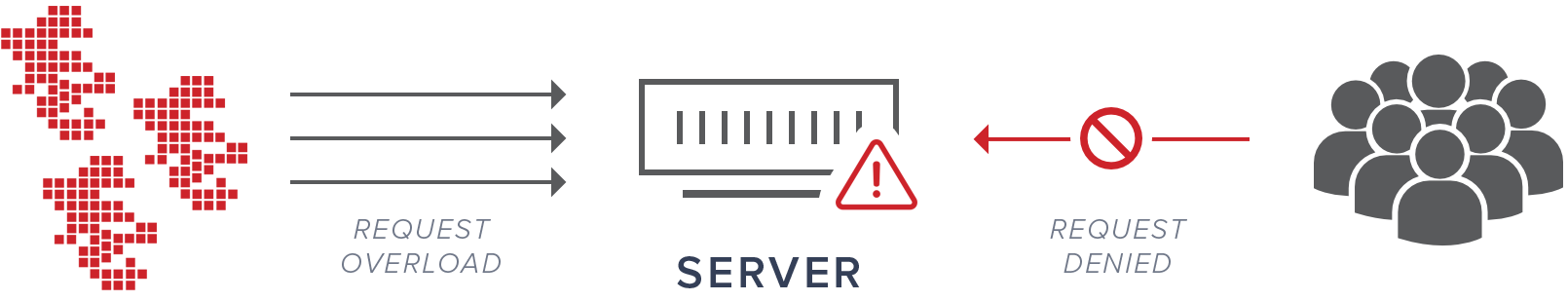
DDoS Protection Overview
According to a research by CDNetworks, more than 54% of businesses were victim of DDoS Attacks in 2017 and even greater number is at risk in 2018. By leveraging on the vulnerabilities within hundreds and thousands of of insecure IoT (Internet of Things) devices, the creation of botnets and subsequent large-scale volumetric attacks is easier and more impactful than ever before. Besides massive scale DDoS Attacks, the focus of attacks is rapidly moving from network & transport layer to application layer 7 where the attacks are way more complex. This means that taking an application or a website offline would require lesser bandwidth and fewer resources resulting in greater disruption and impact on operations. DDoS attacks are able to hamper standard business operations by negatively affecting website availability and performance, sometimes even completely taking them offline. On average, the hourly cost of downtime due to network infrastructure failure is more than USD 100K/hr. One of the obvious side affect of similar attacks is loss of brand reputation, business and customers. In order to combat these complex, massively disruptive attacks, an intelligent, AI-powered scalable network is required which can combat every new type of attack. BlockDoS achieves this by using a global network with more than 150+ PoPs, data-driven intelligence to combat vulnerabilities and exploits and proven scalable unlimited DDoS protection.
Total Protection
150+ Global PoPs
Managed DDoS Protection
Common Type of DDoS Attacks
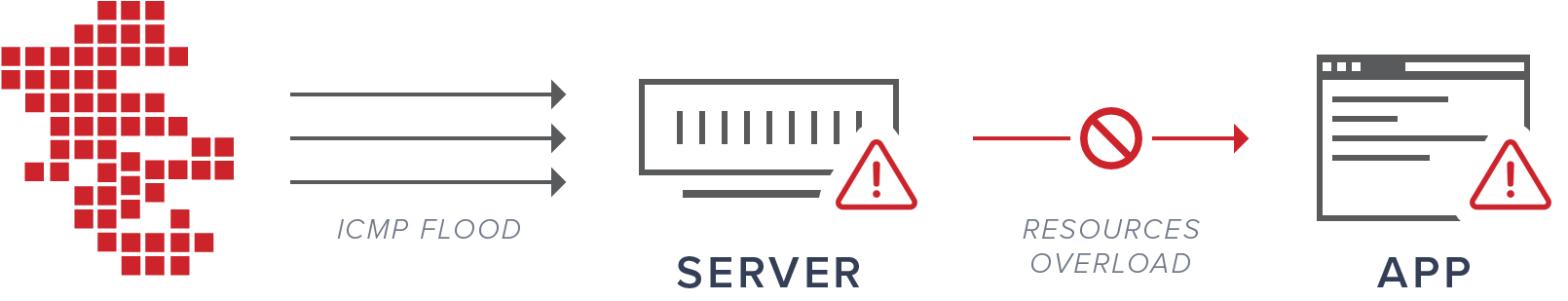
Network Layer Attack (Layer 3)
A common type of Network Layer attack is "ICMP Flood" whereby attacker takes down the system through repeated "pings" (ICMP echo requests).
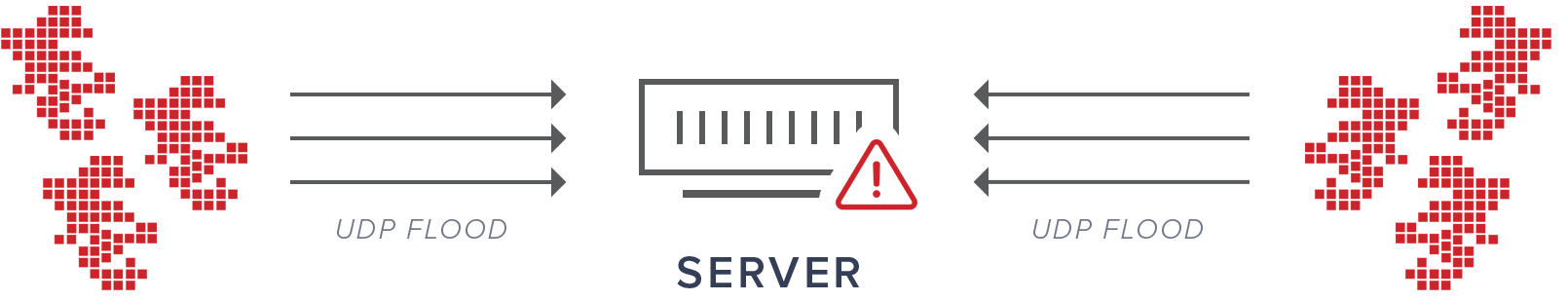
Transport Layer Attack (Layer 4)
The most common attack in Transport Layer is "UDP Flood Attack" which involves a taking down target server with UDP requests from large number of computer systems.
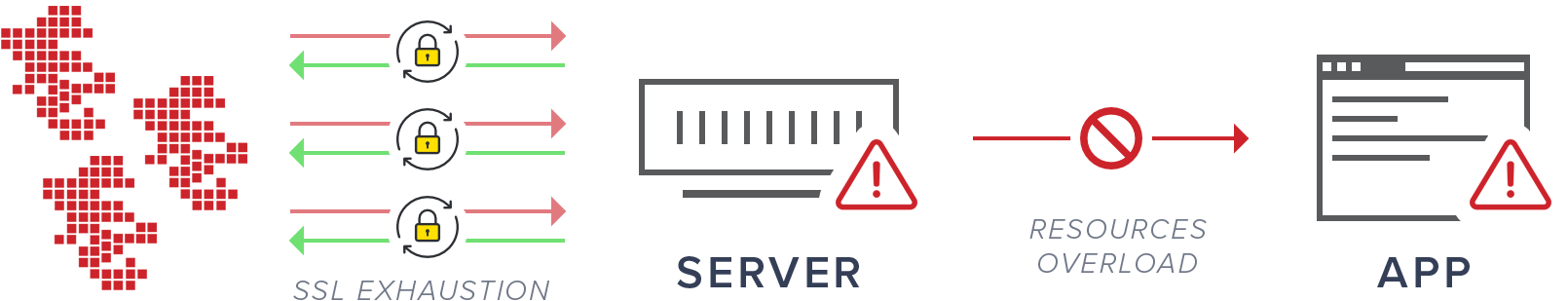
Session (Layer 5) & Presentation Layer Attack (Layer 6)
One of the most common Presentation Layer attack is "SSL exhaustion" whereby a large number of requests are sent to target host to force server to perform resource extensive process for setting up secure sessions.
Application Layer Attack (Layer 7)
A popular Application Layer Attack is "Slowloris" which involves sending a large number of simultaneous requests to target server timed carefully to avoid timeout thereby not leaving room for legitimate requests.
DDoS Attack Glossary
| LAYER 3 - Network |
| ICMP Flood |
| ICMP Fragmentation |
| BGP Hijacking |
| LAYER 4 - Transport |
| IPSec Flood |
| UDP Flood |
| SYN Flood |
| LAYER 5 – Session / LAYER 6 - Presentation |
| SSL Exhaustion |
| Long Lived TCP sessions |
| DNS query floods |
| LAYER 7 - Application |
| Slowloris |
| Slow Post |
| Slow Read |
| HTTP/S Flood |
| CVE Attack Vectors |
| Layer 7 protocol floods (SMTP, DNS, SNMP, FTP, SIP) |
| Database Connection Pool Exhaustion |
| Resource Exhaustion |
| Large Payload POST requests |
| Mimicked user browsing |


